The US and the UK Master’s Part / Chapter-wise Dissertation Writing Service

Then You’ve Certainly Reached the Right place
Hacking and Prevention
Definition of Hacking
According to the Internet Security Systems (n.d), two definitions have been accorded to Hacking. The first one reflects about working with computers either in a professional capacity or for hobby, while the definition for the second refers to breaking into computer systems. The formal definition commonly refers to “cyber criminals” as “crackers” and although it is still used by many computer enthusiasts, it is still considered as older definition. The most commonly used definition is the later one, as it refers to “hackers” particularly those who visit the webpage using the web-server log, while the second one refers about the visiting the web pages as part of searching.
Definition of Prevention
According to Vermont Department of Health, Agency of Human Services (n.d), the definition for prevention is “To prevent” means literally “to keep something from happening”.

Researchers to mentor-We write your Assignments & Dissertation
With our team of researchers & Statisticians - Tutors India guarantees your grade & acceptance!
About serviceHacking
Hackers enter the system like “sword fish” to “matrix” using only a mouse and a keyboard. DSW Shoes, Polo Ralph Lauren and BJs whole sales are the well-known brands that have lost data through the hacking. Social security numbers and credit card number are commonly stolen through computer hacking and not only do they utilize this data for open buying and selling for profit with names like shadowcrew, carderplanet, dark profit, network terrorism forum. They hack the username and password, which are left by the user without signing off; this presents an opportunity for hackers, where they will hack these usernames and passwords. Similarly, emails are hacked using spywares / malwares, by tracing cookies entries and when the system of security islow, via DNS and static IP, hackers, hack the website database
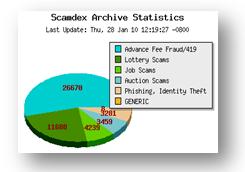
Percentage of Hacking
Prevention of Hacking
Several preventive measures had been taken for the prevention of Hacking and following are the preventive measures;
- System should be hardened in terms of security tightening or through lock down for better security either using required software, software that are unnecessary should be deactivated, any daemons that are not used should be disabled, and at last to increase security base operating system should be utilized
- All system should be patched as through holes, intruders could gain access thus, it is better to keep track of all these patches and those programs that are found to be vulnerable should be avoided.
- Firewalls such as software (e.g. Zonealarm) or hardware (e.g. Symantec) should be installed on the network or on the system as they have an ability to block and also detect scan attempts as they work at the packet level.
- Network security should be assessed and following are the few suggestions in order to assess the network security include:
- To enable us to see the services that are exposed, network should be port scanned.
- Servers need to be checked through vulnerability scanner
- Firewall logs need to be checked
- Network traffic needs to be monitored
- Passwords should be
- Significance (example, could be birth dates)
- For all your accounts maintain similar passwords
- Connection should be encrypted meaning, server and client encryption
- Telnet, FTP or POP should not be used unless passwords are strongly encrypted.
- Instead of Telnet or FTP, try to utilize the SSH
- Avoid sending information that is sensitive in nature.
- Server access should be limited
- Regular scanning of system, using software such as anti-virus (example, Norton or McAffee)
References
Internet Security Systems (n.d). Hacking. Retrieved online on March 3, 2010, from the website http://www.iss.net/security_center/advice/Underground/Hacking/default.htm
Vermont. Department of Health. Agency of Human Services. A Vermont Government Webiste. Retrieved online on March 3, 2010, from the website http://healthvermont.gov/adap/prevention/prevention_fact.aspx
Crucial Paradigm Webs Solutions (2010). Crucial Paradigm. Retrieved online on March 3, 2010, from the website http://www.crucialp.com/resources/tutorials/website-web-page-site-optimization/hacking-attacks-prevention.php
Scamdex: The Internet Scam Resource Since 2003. Scamdex mail scam resource Retrieved online on March 3, 2010, from the website

Full Fledged Academic Writing & Editing services
Original and high-standard Content
Plagiarism free document
Fully referenced with high quality peer reviewed journals & textbooks
On-time delivery
Unlimited Revisions
On call /in-person brainstorming session
More From TutorsIndia
Coursework Index Dissertation Index Dissertation Proposal Research Methodologies Literature Review Manuscript DevelopmentREQUEST REMOVAL


